
PROCESSING. PLEASE WAIT...

White Paper: SPECOPS
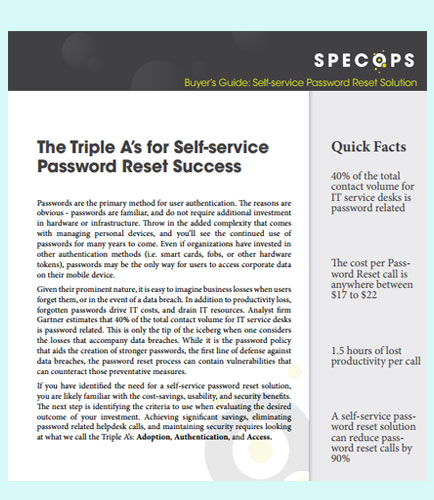
If you have identified the need for a self-service password reset solution, you are likely familiar with the cost-savings, usability, and security benefits. The next step is identifying the criteria to use when evaluating the desired outcome of your investment.
A self-service password reset and management solution not only reduces the number of help desk password tickets but also enhances the productivity of an end user by averting unnecessary and prolonged waits.
This whitepaper provides insights for achieving significant savings and maintaining security requires looking at what we call the Triple A’s: Adoption, Authentication, and Access.
The right balance is attainable with a solution that is:
• Easy to adopt - with various enrollment options
• Highly accessible - no matter the device and location
• Secure yet flexible - permits multifactor authentication with authentication choice
• Cost effective - uses existing assets such as Active Directory, mobile devices, and authentication devices.
By: SPECOPS
With password security policies and best practices in constant flux, our effectiveness in safeguarding our organization requires scrutiny. Unfortunately, the regulatory bodies we must abide by do not always pave a clear direction. This is where our own judgment must fill in the gaps. When it comes to password security policy, it is always a good rule of thumb to take a segmented approach over a generalized one. This whitepaper provides insights on how to create a strategy for password policies, while continuing to meet today’s compliance requirements. Key takeaways from this whitepaper: Character compositions and knowledge-based authentication Forced password expiration Compliance requirements in the backdrop of current wisdom about secure passwords Future-proofing existing password policies Password expiration based on role
By: SPECOPS
Passwords are the thin layer protecting our personal information from the “unknown.” A few key proactive measures can make that layer impenetrable. Shifting some burden from individuals to password policies that promote stronger passwords is the next logical step. A proactive password security approach can go a long way for both organizations and users. Password security is a responsibility that we must embrace and act on. When knowledge is combined with action, prevention is a natural outcome. This whitepaper helps to understand the correlation between publicized password leaks and the importance of blocking such passwords when guiding organizations and individuals towards stronger password security. Key takeaways from this whitepaper: Predictable Pitfalls: A strong password takes a backseat to a memorable password Data breaches and password dictionaries: creates opportunities in the form of dictionary attacks Turning the tables: Every data breach has a silver lining


 2026 All Rights Reserved | by: www.ciowhitepapersreview.com
2026 All Rights Reserved | by: www.ciowhitepapersreview.com