
PROCESSING. PLEASE WAIT...


White Paper: Qualys
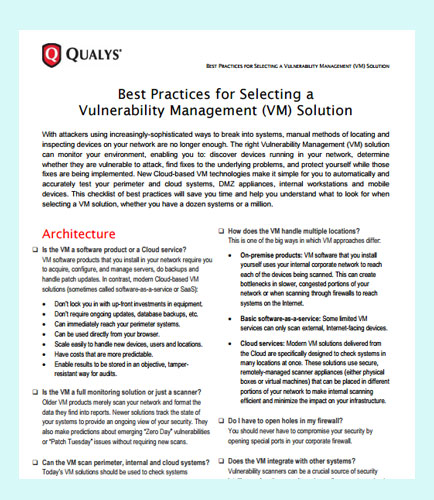
A complete Vulnerability Management (VM) solution can monitor your environment, enabling you to discover devices running in your network, and determine whether they are vulnerable to attack.
The VM solution helps you to find fixes to the underlying problems, and protect yourself while those fixes are being implemented.
This whitepaper provides insights on the best practices that will save you time and help you understand what to look for when selecting a VM solution, whether you have a dozen systems or a million.
It addresses key questions like:
Is the Vulnerability Management a software product or a Cloud service? How does the VM handle multiple locations?
What are the top features to look for in VM scanning? Can the VM use authentication for deeper scanning?
Can the Vulnerability Management tailor reports to different audiences? Does the VM offer predictive analysis?
What information about the underlying cause does the VM provide about each vulnerability?
By: Qualys [NASDAQ: QLYS]
Today, the cloud-based security services are expected to be a “new area of growth.” The adoption of cloud solutions is driven by the need to innovate, simplify and cut costs. Avoiding the cost and the complexity of traditional software is one of the reasons why cloud services has become a mainstream delivery method for security solutions. This whitepaper explains how you can use cloud-based security to protect your network and ensure compliance without breaking the bank. Key takeaways from this whitepaper: Why smaller organizations are vulnerable Common approaches to security are too expensive Cloud-based security is more affordable & effective Seizing other benefits of cloud-based security Continuous security and compliance solutions
By: Qualys [NASDAQ: QLYS]
Small- to medium-sized businesses that have limited budgets can create strong security by performing proper analysis and focusing on high-risk areas. The steps to stronger security in small businesses can be easier and less expensive to implement than you might think. Hence, this will help you to identify the highest-risk areas in order to focus your remediation efforts for strong security. This whitepaper provides actionable controls you can implement to increase SMBs security in a cost-effective manner by targeting well-known risk areas from the start. Six steps to stronger cyber security in small and medium businesses: Keep an accurate hardware inventory Keep an accurate software inventory Actively manage configurations Remediate vulnerabilities quickly Automate endpoint defenses Control administrative access


 2025 All Rights Reserved | by: www.ciowhitepapersreview.com
2025 All Rights Reserved | by: www.ciowhitepapersreview.com